How thieves gain access to your data center

When someone breaks into a home or shop and steals items of value, the results are upsetting and distressing to one or more individuals. But when thieves gain access to servers in a data center (either through cyber-attacks or physical attacks), the results can be devastating on a global scale. There’s the potential for extensive loss of very personal, sensitive information from people across the world.
For data center managers, this type of attack not only causes fines and damage to equipment, it also damages the company’s public reputation. People are putting trust into data center operators to protect their information and require data center managers to do everything in their power to keep this data secure.
The first step to helping prevent data center theft? Understanding how thieves gain access to your data center and information on your servers.
Physical data center security breaches
Mistakes do happen – and it’s important to share so we learn from them all the time. Factors such as your emotional state and tiredness can affect your judgement. Thieves often make it their duty to learn about members of staff, to build an understanding of their schedules, passwords and routines, and to take advantage of any vulnerabilities.
There have been many instances where thieves have been aided in accessing a data center by gaining access to valid swipe cards and learning staff passwords. Unfortunately, there are also occasions of internal sabotage, where members of staff have willingly collaborated to aid the thief. It’s important to perform thorough checks on potential staff members and to ensure all employees are briefed to report any strange behaviour/to challenge unauthorised personnel when safe to do so.
One well-known data breach involved thieves dressing up as police officers to inform members of staff there were reports of people on the roof. By posing as trusted members of authority, these fake officers gained access, attacking and restraining members of staff along the way. When in doubt, even if identification is present, call the local police authority and ask for confirmation of badge numbers.
Other ways of gaining access have involved using extensive tooling/high-power equipment to breach security walls and breaking in through emergency doorways. Most of the time, some insider knowledge is used to do this.
Preventing physical data center security breaches
While training your staff and providing regular security briefings can help, it’s important to evaluate the physical barriers you have in place to check they are fit to withstand aggressive attack.
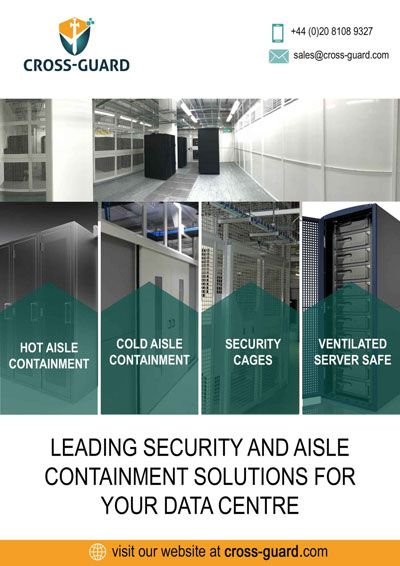
Cross-Guard can help. The company offers a wide range of security cages that are high-strength and resistant to attack. Connexions data center cages are not only strong, but also very versatile, allowing you to create a secure caged area even in a very challenging environment. If you don’t think a cage will fit, don’t leave the area unsecured – give the Cross-Guard team a ring to see if they can help.
Cross-Guard also offers Extendor security cages. These are market-leading and certified to withstand attack from a large variety of tools. Cross-Guard’s Extendor Eclipse is the strongest and most robust on the market, certified to Security Rating 3 by the LPCB. In addition to caging, Cross-Guard can offer bespoke, high-security walling.
Cyber security breaches of data centers
Of course, the flip side of physical security is cyber security. Perhaps gaining more media attention, cyber security is equally as important as physical security. Sometimes, a thief doesn’t need to necessarily set foot in your data center to steal personal, valuable information.
Virtual threats such as viruses and worms are becoming more sophisticated. Malicious attacks can also take advantage of weak, default and stolen passwords. Phishing emails are sent frequently and, where some are obvious, others can look very genuine.
Preventing cyber security breaches of data centers
Ensuring top range virus protection is the first step. The next comes down to making sure staff are briefed and know easily how to spot phishing emails or anything suspicious. Try to keep updated with what’s going on in terms of other data breaches and how hackers are advancing. It’s important that you stay one step ahead of them.
To conclude, there are a number of opportunities thieves can exploit to gain access to your data center. Make sure staff are fully checked and briefed, invest in high-strength security measures for perimeter and internal security, and ensure you have up-to-date virus software protecting IT equipment.
If you need any further information, or would like a quote for Cross-Guard’s security cages or other products, you can always give us a ring on 020 8108 9328 or email sales@cross-guard.com.
SHARE